In today’s hyper-connected world, staying invisible online has become more of a necessity than a choice. Every click, search, purchase, and login leaves behind a digital footprint that can be tracked, analyzed, and sometimes misused. With increasing cyber threats, data leaks, and identity theft incidents, users are searching for smarter ways to regain control of their privacy. This is where advanced cybersecurity tools like Surfshark step in, offering a powerful shield for identity, data, and digital life across all devices.
Below is a deep exploration of how modern online invisibility works and how cybersecurity solutions are reshaping digital privacy in a connected world.
Rethinking Digital Privacy In A Hyperconnected Era
The modern internet is built on convenience, but that convenience often comes at the cost of privacy. Every website you visit collects data, every app you use tracks behavior, and every online service stores personal information. Over time, this creates a detailed digital identity that exists far beyond your control.
Staying invisible online does not mean disconnecting from the internet. Instead, it means reducing exposure, limiting data leaks, and controlling who can access your information. Cybersecurity platforms like Surfshark are designed to help users rebuild this balance between connectivity and privacy.
One of the biggest challenges today is that data collection is often invisible to the user. Background tracking scripts, cookies, and hidden analytics tools work silently while users browse freely. This leads to targeted ads, behavioral profiling, and in some cases, unauthorized data sharing.
Modern privacy protection focuses on breaking this chain of exposure. By encrypting internet traffic, masking IP addresses, and blocking trackers, users can significantly reduce how much information they reveal online. The goal is not isolation but intelligent protection, where users decide what to share and what to hide.
As awareness grows, digital privacy is shifting from a technical concern to a personal priority. People are no longer comfortable being constantly observed online, and tools that restore anonymity are becoming essential rather than optional.
How Advanced Cybersecurity Tools Build Invisible Digital Shields
At the core of staying invisible online is encryption technology. Encryption transforms readable data into secure code that cannot be interpreted without the correct key. When users connect through secure cybersecurity tools, their data becomes unreadable to hackers, internet providers, or third-party trackers.
Platforms like Surfshark create secure tunnels between the user’s device and the internet. This means that online activity is hidden from external observation. Instead of revealing your actual location and identity, your digital presence is masked through secure servers.
Another key feature is IP masking. Every device connected to the internet has an IP address, which acts like a digital identifier. This address can reveal location, browsing habits, and even device information. By replacing the real IP with a virtual one, users can browse anonymously without leaving traceable signals.
Advanced cybersecurity systems also include tracker blocking. Websites often use hidden trackers to follow users across different platforms. These trackers build behavioral profiles that are later used for advertising or data analysis. By blocking them, users regain control over their digital behavior.
What makes modern cybersecurity tools powerful is their ability to work silently in the background. Users do not need technical knowledge or manual configuration. Protection happens automatically, ensuring that privacy is maintained at all times.
The idea of invisibility online is no longer about hiding completely but about controlling visibility. Users choose when, where, and how their data is shared, creating a safer and more predictable digital environment.
Identity Protection Across Devices And Everyday Digital Life
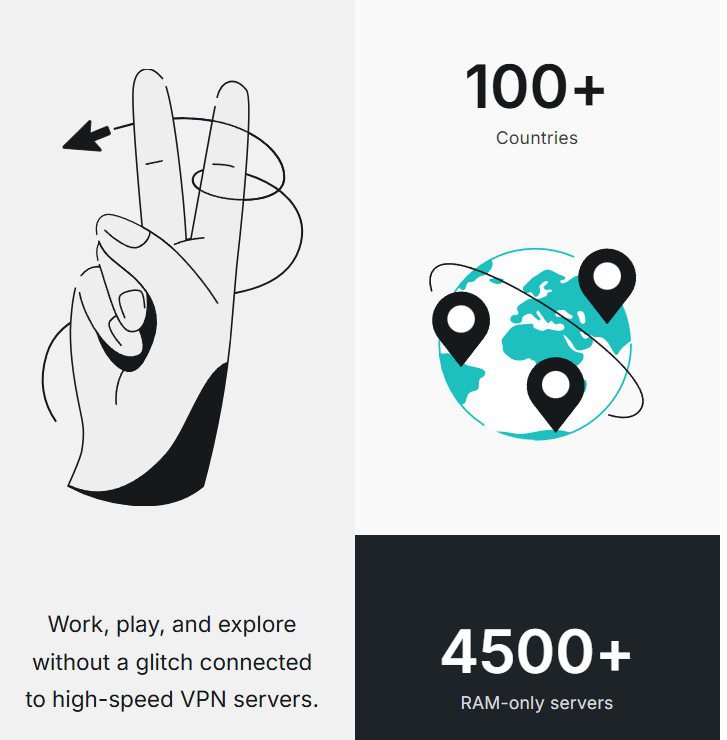
Digital life today is not limited to a single device. People switch between smartphones, laptops, tablets, and smart devices throughout the day. Each of these devices becomes a potential entry point for cyber threats if not properly protected.
One of the strongest advantages of modern cybersecurity platforms is cross-device protection. Instead of securing only one device, they extend protection across all connected systems. This ensures that whether a user is working, shopping, streaming, or browsing, their identity remains secure.
Identity protection involves safeguarding personal information such as login credentials, banking details, email accounts, and social media profiles. Cybercriminals often target weak points in this data chain to gain unauthorized access.
Advanced security tools monitor network behavior and detect unusual activity patterns. If a suspicious connection attempt is detected, it is automatically blocked before any damage can occur. This proactive approach is essential in preventing identity theft.
Another important aspect is secure browsing on public networks. Public Wi-Fi connections in cafes, airports, and hotels are often unprotected and vulnerable to interception. Without encryption, sensitive data can easily be captured by attackers. Cybersecurity tools eliminate this risk by creating secure encrypted tunnels even on unsecured networks.
Digital identity is no longer just a login credential; it represents a person’s entire online existence. Protecting it requires constant vigilance and intelligent systems that adapt to evolving threats. Cross-device security ensures that no matter where users connect from, their identity remains protected.
The Hidden Risks Of Data Exposure And Online Tracking
Most users underestimate how much of their personal information is exposed during daily internet use. Even simple actions like browsing a website or clicking an ad can reveal significant data about preferences, location, and behavior patterns.
Online tracking is one of the most widespread forms of data collection. Companies use cookies, pixels, and scripts to follow users across different websites. Over time, this builds a detailed behavioral profile that can be used for advertising, analytics, or in some cases, unauthorized data sharing.
The real risk of tracking is not just targeted advertising but long-term data accumulation. Once information is collected, it often remains stored indefinitely, creating a permanent digital record of user behavior.
Data exposure also increases vulnerability to cyberattacks. When personal information is widely available online, hackers can use it for phishing, identity theft, or account breaches. Even small data leaks can lead to significant security risks when combined with other exposed details.
Cybersecurity solutions help reduce this exposure by limiting what information is visible online. By hiding IP addresses, blocking trackers, and encrypting traffic, users reduce the amount of data available for collection.
Another hidden risk comes from unsecured applications and background processes. Many apps collect data even when they are not actively in use. Without proper protection, this information can be transmitted without user awareness.
The key to reducing these risks lies in minimizing digital exposure. The less information available, the harder it becomes for malicious actors to build profiles or launch attacks. Modern cybersecurity tools act as a barrier between users and the data-hungry internet ecosystem.
Building A Safer And More Private Digital Future
The future of the internet is moving toward greater connectivity, but also greater surveillance. As technologies like artificial intelligence, smart devices, and cloud computing expand, the volume of data being generated continues to grow exponentially.
In this evolving landscape, digital privacy will depend heavily on proactive protection strategies. Users can no longer rely solely on default security settings or basic antivirus tools. Instead, they need comprehensive solutions that address multiple layers of exposure.
Cybersecurity platforms like Surfshark are designed to evolve with these changes. They combine encryption, anonymity, and threat detection into a single system that protects users continuously. This ensures that privacy is not a temporary state but an ongoing condition.
A safer digital future also depends on awareness. Users must understand how their data is collected, stored, and used. Once this awareness is established, it becomes easier to make informed decisions about online behavior.
The concept of invisibility online will continue to grow as people seek more control over their digital lives. It is not about avoiding technology but about using it safely and intelligently.
As cybersecurity tools become more advanced, they will play a crucial role in shaping how people interact with the internet. From securing personal identities to protecting sensitive data across devices, these tools are becoming essential guardians of digital freedom.
In the end, staying invisible online is about empowerment. It is about giving users the ability to decide what they share, when they share it, and who can see it. With the right protection in place, the digital world becomes not only more secure but also more private, balanced, and user-controlled.